Alleged Iranian nation-state hacker group Tortoiseshell performed a watering hole attack on several shipping and logistics websites in Israel to collect information about their users. Attackers stay hidden by impersonating the genuine jQuery JavaScript framework. Organizations are urged to raise awareness for watering hole attacks and always keep the systems updated.
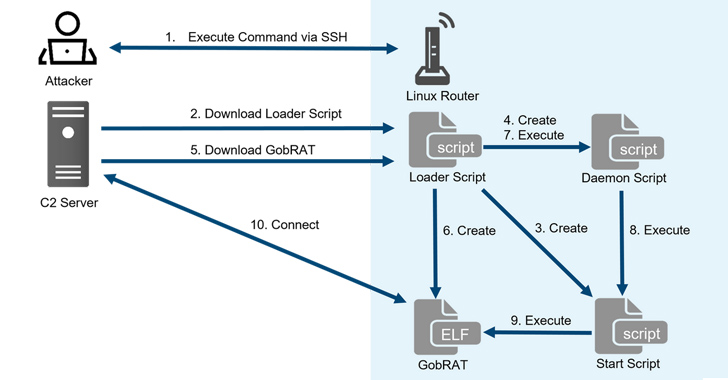
“Initially, the attacker targets a router whose WEBUI is open to the public, executes scripts possibly by using vulnerabilities, and finally infects the GobRAT,” the JPCERT Coordination Center (JPCERT/CC) said in a report published today.
The AHA is urging federal regulators to back off from recent guidance that treats patient IP addresses as PHI, saying that the new rules would “reduce public access to credible health information” and create hardships for doctors and hospitals.
The indictment accuses the four FinFisher executives, identified only with an initial, of evading export controls by selling the FinSpy hacking tool to Turkey’s intelligence agency in 2015 through a Bulgarian front company.
OneMain Financial Group, which specializes in issuing loans to people with “nonprime” credit histories, will pay a $4.25 million penalty in New York state for cybersecurity lapses found during a government investigation.
A number of individuals from Armenia contacted the digital rights organizations CyberHUB-AM, an Armenian organization, and Access Now to check their devices for evidence of such spyware.
The Department of Defense announced on Friday that it submitted its classified 2023 cyber strategy to Congress “earlier this week” and plans to release an unclassified summary of its new cybersecurity approach “in the coming months.”
An upstate New York medical specialty practice told regulators that hackers compromised the personal and protected health information of nearly 224,500 employees and patients in an incident discovered in March.
Latitude was able to process transactions during the incident, but “account originations and collections were closed or severely restricted.” The company has since fully recovered, it says.
An unidentified threat actor group has been observed employing a malicious Windows kernel driver in targeted attacks, primarily focusing on the Middle East region. Fortinet security experts have dubbed the artifact as WINTAPIX (WinTapix.sys). To stay protected, users are suggested to immediately implement the driver blocklist feature in Windows to block malicious drivers.