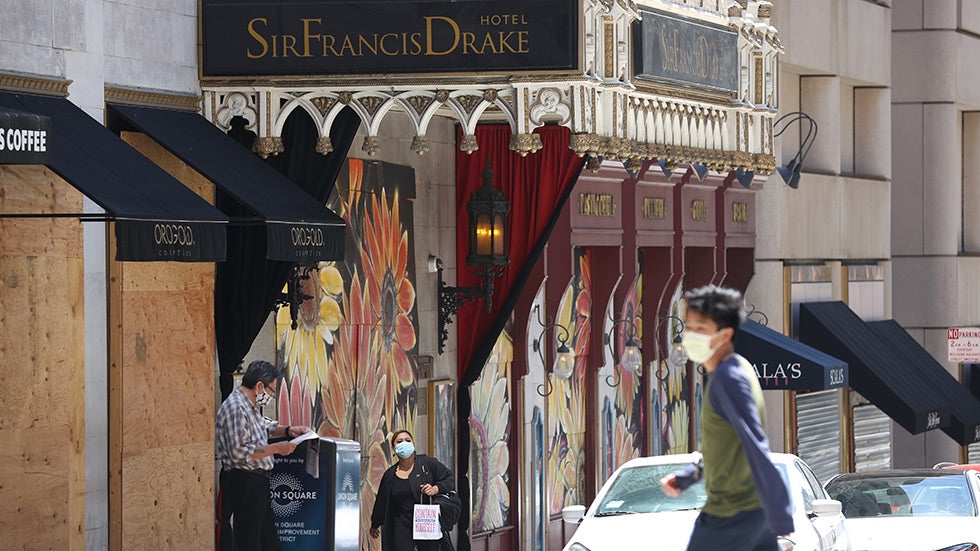
Fraudsters from countries like China, Nigeria, and Russia buy stolen personal information online from previous identity thefts and then use it to make bogus claims on state unemployment systems.
“COVIDGuardian”, the first automated security and privacy assessment tool, tests contact tracing apps for potential threats such as malware, embedded trackers, and private information leakage.
An AOL email phishing campaign is underway to steal users’ login name and password by warning recipients that their account is about to be closed if they do not login and verify it within 72 hours.
The domains *.gvt1.com and *.gvt2.com, along with their subdomains, are owned by Google and typically used to deliver Chrome software updates, extensions, and related content.
Cybercriminals are very persistent and the daily numbers of cyberattacks show no sign of decreasing. This can jeopardize the reputation of students and academics as well as the institution itself.
Armorblox, a cybersecurity startup using natural language understanding to protect enterprise communications, today announced that it raised $30 million in series B venture capital funding.
Targeted entities include hospitals, medical companies, pharmaceutical manufacturers, and energy firms involved in the COVID-19 supply chain.
Malwarebytes spots a new threat group dubbed LazyScripter that targets the International Air Transport Association (IATA) members, airlines, and refugees to Canada.
Akamai finds a long-running cryptomining botnet campaign wherein hackers exploit BTC blockchain transactions to evade detection by the security systems in place.
Palo Alto Networks found a highly sophisticated malware potentially linked to the BlackTech hacking group. It has features and behavior that strongly resembles the WaterBear malware family.