Internet of Things devices are highly susceptible to attacks, breaches, and flaws emanating from issues within the TCP/IP network communications architecture. Here’s an overview of what you need to know to mitigate risks.
On the heels of a previously-reported cyberattack on the European Medicines Agency (EMA), cybercriminals have spilled compromised data related to COVID-19 vaccinations onto the internet.
Dubbed Rogue, the Trojan is the work of Triangulum and HeXaGoN Dev, known Android malware authors that have been selling their malicious products on underground markets for several years.
A watchdog agency for the U.S. Census Bureau says that proper information-technology security safeguards weren’t in place leading up to the start of the 2020 census last year.
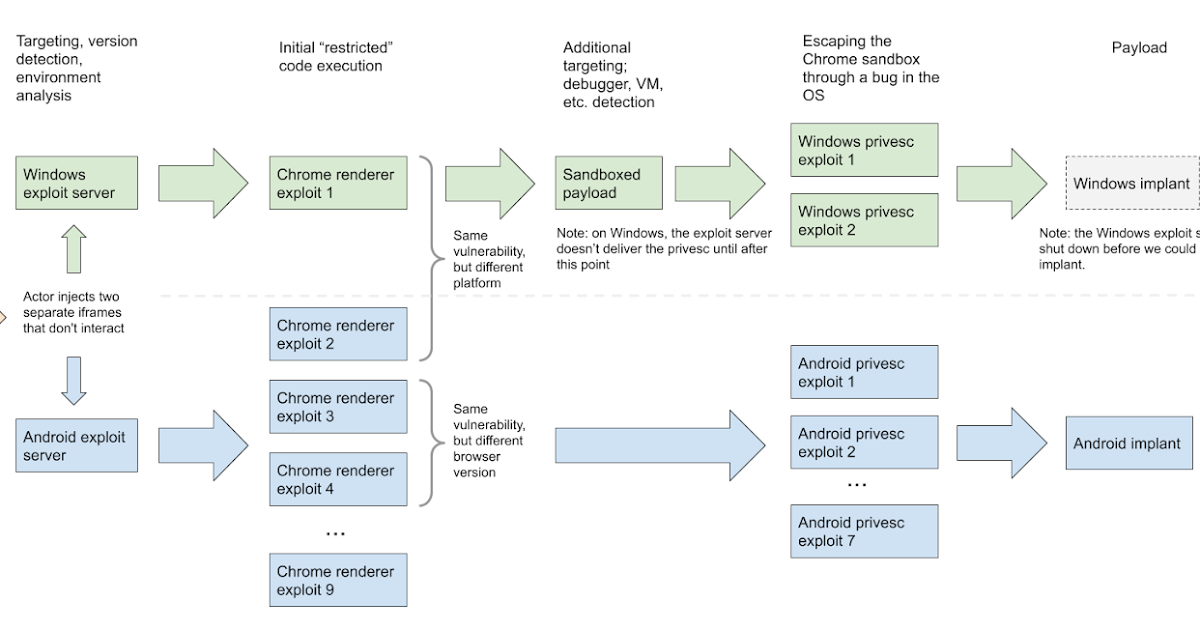
Researchers discovered two exploit servers delivering different exploit chains via watering hole attacks. One server targeted Windows users, the other targeted Android devices.
The issue lies within Spring’s Application-Level Profile Semantics (ALPS) feature which is defined as “a data format for defining simple descriptions of application-level semantics”.
SAP has published 10 advisories to document flaws and fixes for a range of serious security vulnerabilities. SAP also published a total of 7 other updates for previously released security notes.
The company now says that the personal data of up to 400,000 of its customers was compromised in the ransomware attack last November — 40,000 more than the company originally thought.
The website claims to be selling Microsoft source code and repositories for $600,000. Microsoft confirmed that threat actors accessed their source code during their SolarWinds breach.
A Mimecast-issued certificate used to authenticate some of it’s products to Microsoft 365 Exchange Web Services has been “compromised by a sophisticated threat actor,” the company has announced.