While similar to IcedID, Proofpoint researchers confirmed it is an entirely new malware, likely created by the IcedID developers. Latrodectus shares infrastructure overlap with historic IcedID operations.
First encountered in December 2019, JsOutProx is a RAT and highly obfuscated JavaScript backdoor that allows its operators to run shell commands, download additional payloads, execute files, capture screenshots, establish persistence, and more.
A very recent malvertising campaign was found impersonating the popular VPN software NordVPN. A malicious advertiser is capturing traffic from Bing searches and redirecting users to a decoy site that looks almost identical to the real one.
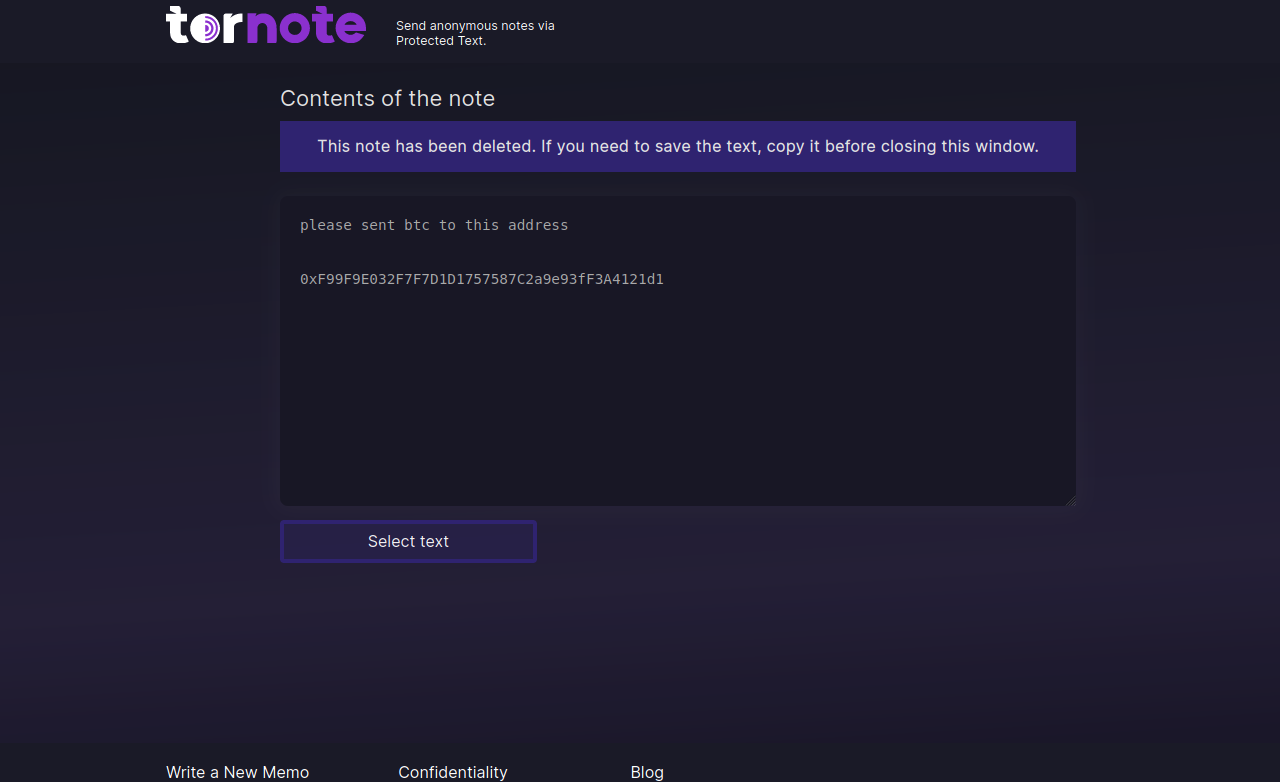
A cybercrook who has been setting up websites that mimic the self-destructing message service privnote.com accidentally exposed the breadth of their operations recently when they threatened to sue a software company.
In January 2024, FortiGuard Labs collected a PDF file written in Portuguese that distributes a multi-functional malware known as Byakugan. While investigating this campaign, a report about it was published.
A premium WordPress plugin named LayerSlider, used in over one million sites, is vulnerable to unauthenticated SQL injection, requiring admins to prioritize applying security updates for the plugin.
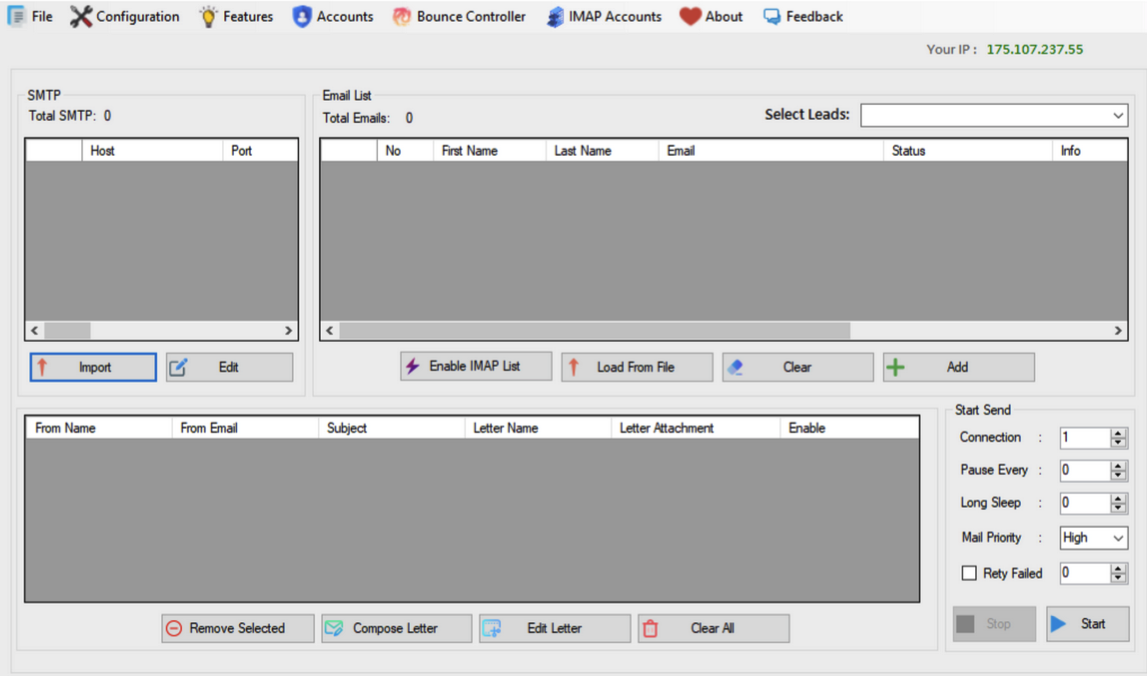
The core brand of The Manipulaters has long been a shared cybercriminal identity named “Saim Raza,” who for the past decade has peddled a popular spamming and phishing service variously called “Fudtools,” “Fudpage,” “Fudsender,” “FudCo,” etc.
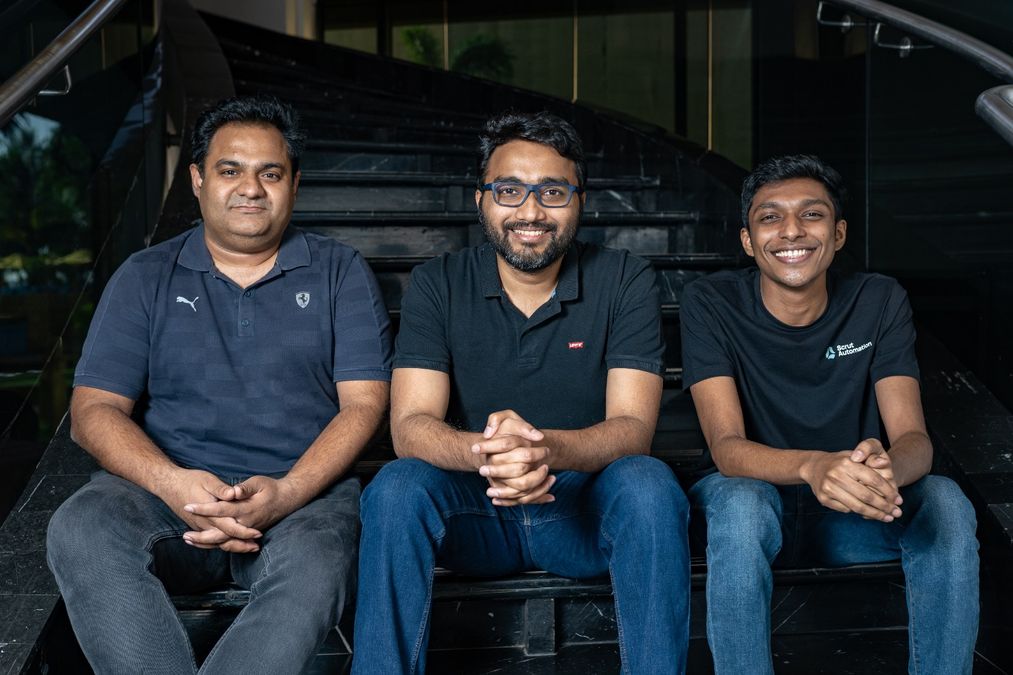
Scrut Automation, a GRC platform provider, has announced today that it secured $10 million in growth capital from its existing investors, including Lightspeed, MassMutual Ventures, and Endiya Partners.
Chilean data center and hosting provider IxMetro Powerhost has suffered a cyberattack at the hands of a new ransomware gang known as SEXi, which encrypted the company’s VMware ESXi servers and backups.
A persistent social engineering threat faced by enterprises involves attackers trying to obtain login credentials for identity and access management (IAM), cloud resources, or single sign-on (SSO)-enabled systems.