Threat group Water Curupira, known for its Cobalt Strike backdoors, recently transitioned to using Pikabot malware in phishing campaigns. Pikabot witnessed a surge in activity in Q4 2023, potentially serving as a replacement for Qakbot after its takedown. Users must exercise caution with email attachments and verify sender authenticity.
The breach occurred in August 2023 when threat actors gained unauthorized access to a company server and stole unencrypted files containing medical records, personal information, and employment records.
A 22-year-old French hacker has been sentenced to three years in U.S. federal prison for his involvement in the ShinyHunters hacking group and must pay $5 million in restitution.
A stored XSS flaw in the Popup Builder WordPress plugin has been exploited by the Balada Injector campaign. The campaign injects malicious code into websites using older versions of the plugin, with over 6,200 sites currently affected.
Seattle-based company ExtraHop has raised $100 million in growth capital for its cloud-native network detection and response platform. The funding will be used to expand operations and business reach.
The malware’s obfuscation and custom code suggest mature threat actors, but the inclusion of childish elements complicates attribution, making it difficult to determine the exact nature of the operation.
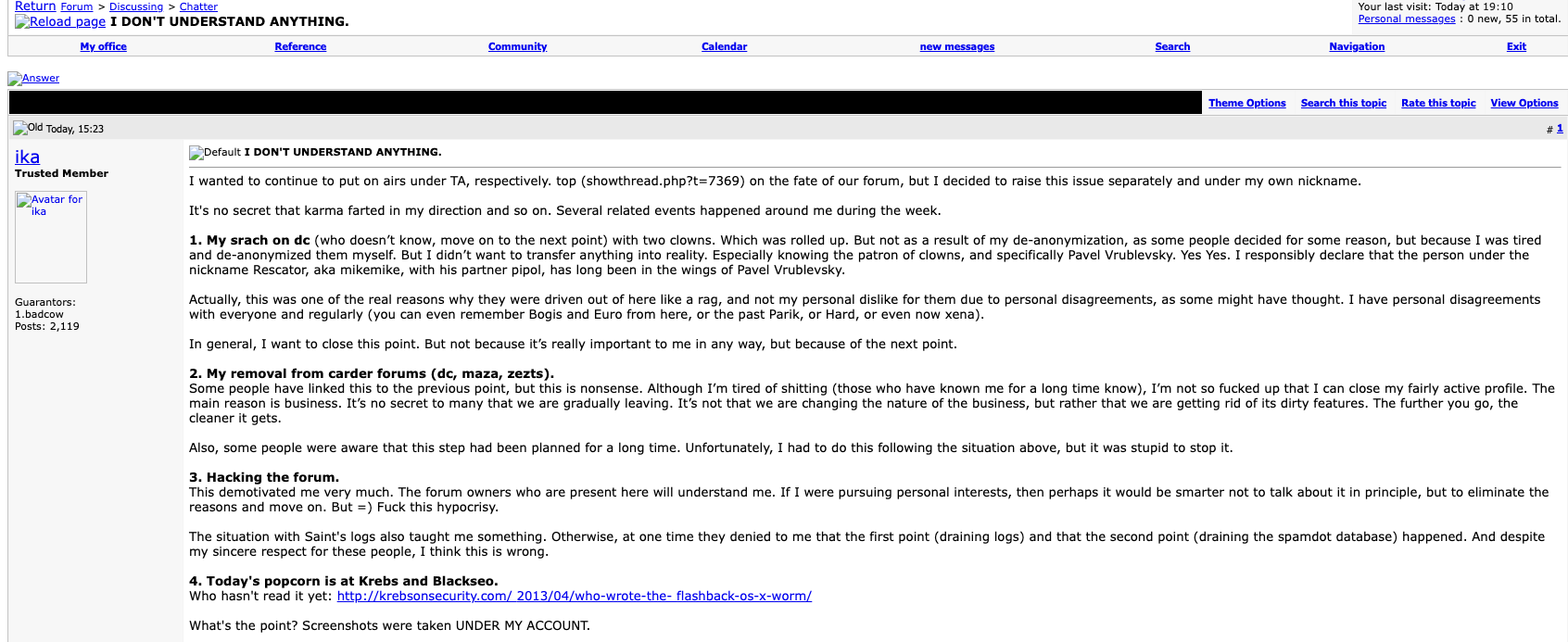
Two Russian men, known as Icamis and Salomon, co-ran the top spam forum Spamdot and worked closely with dangerous cybercriminals, controlling botnets and harvesting passwords.
Last week, Tigo Business, a division of Paraguay’s largest mobile carrier, suffered a cyberattack that impacted their cloud and hosting services. While it did not confirm the attack, reports suggest that it was targeted by the Black Hunt ransomware.
The US Department of Justice expects an increase in government disruption operations in cybersecurity in 2024, with a focus on dismantling cybercriminal infrastructure and targeting individuals and companies supporting cybercrime.
The vulnerability permits any unauthenticated user to upload arbitrary files, including potentially malicious PHP files, which could lead to remote code execution on the affected system.