The Royal ransomware gang, now known as BlackSuit, has undergone a strategic rebranding, unveiled in a joint advisory by CISA and the FBI. This shift, observed since November 2022, involves advanced encryption methods and sophisticated attack vectors, emphasizing the exploitation of vulnerabilities in public-facing applications and remote desktop protocols.
TA402 has recently employed a new initial access downloader called IronWind, using various infection chains and delivery methods such as Dropbox links, XLL and RAR file attachments, in order to evade detection.
The attackers utilize deceptive tactics, such as sending archive files disguised as PDFs, to trick victims into launching malicious executables and gain unauthorized access to their accounts.
The Medusa ransomware gang demanded a $6 million ransom, but Moneris stated that its security team stopped access to critical data and no ransom request was made. The company didn’t disclose when the breach was attempted or whether it paid a ransom.
Hackers linked to the Russian GRU targeted Danish critical infrastructure, exploiting vulnerabilities in Zyxel firewalls and demonstrating meticulous planning and coordination.
DP World is working to restore normal operations and investigate the possibility of data access and theft, engaging with cybersecurity experts and the Office of the Australian Information Commissioner.
Customer bank accounts and credit card numbers may have been affected, as well as the bank account information of some suppliers. The incident primarily affected the company’s dental and medical distribution operations in North America and Europe.
Juniper Networks confirmed that successful exploitation of the vulnerabilities can lead to pre-authenticated remote code execution, and recommends disabling J-Web or limiting access to trusted hosts as a workaround.
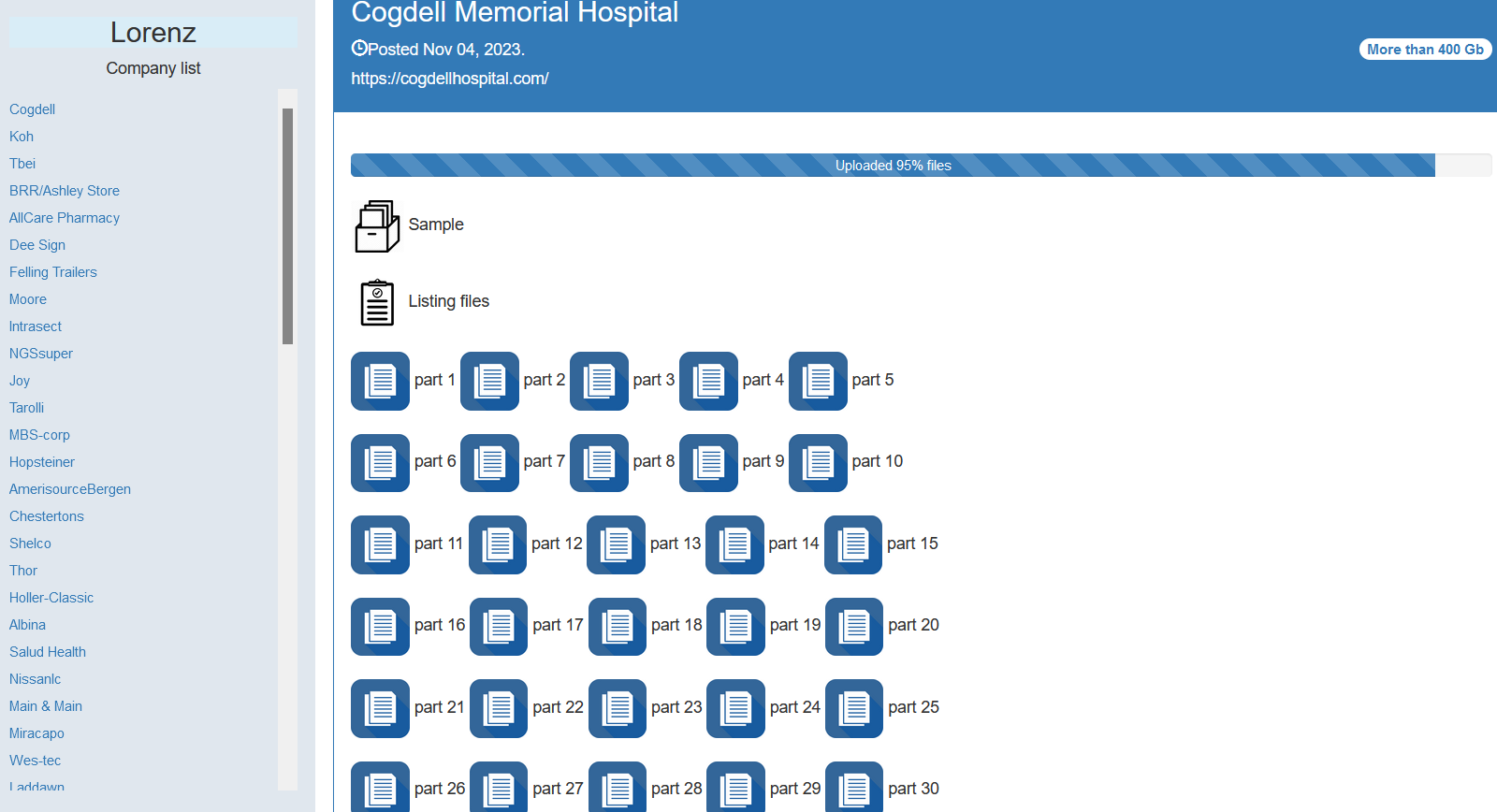
The Lorenz extortion group has targeted and leaked data from the Texas-based Cogdell Memorial Hospital, adding to the rising number of ransomware attacks on healthcare organizations in the US.
The leaked data includes personal details such as full names, email addresses, usernames, and profile links, posing a significant threat to Chess.com users for potential identity theft and phishing attacks.