The acquisition aligns with Proofpoint’s vision of securing the human layer in cybersecurity and aims to improve email security, reduce the risk of data breaches, and ease the workload on security teams.
Researchers uncovered a phishing campaign distributing the Remcos remote access trojan. Cybercriminals disguised the malware as a payslip in a deceptive email. Remcos RAT can perform a range of malicious activities, including keylogging, capturing screenshots, controlling webcams and microphones, and extracting browser histories and passwords.
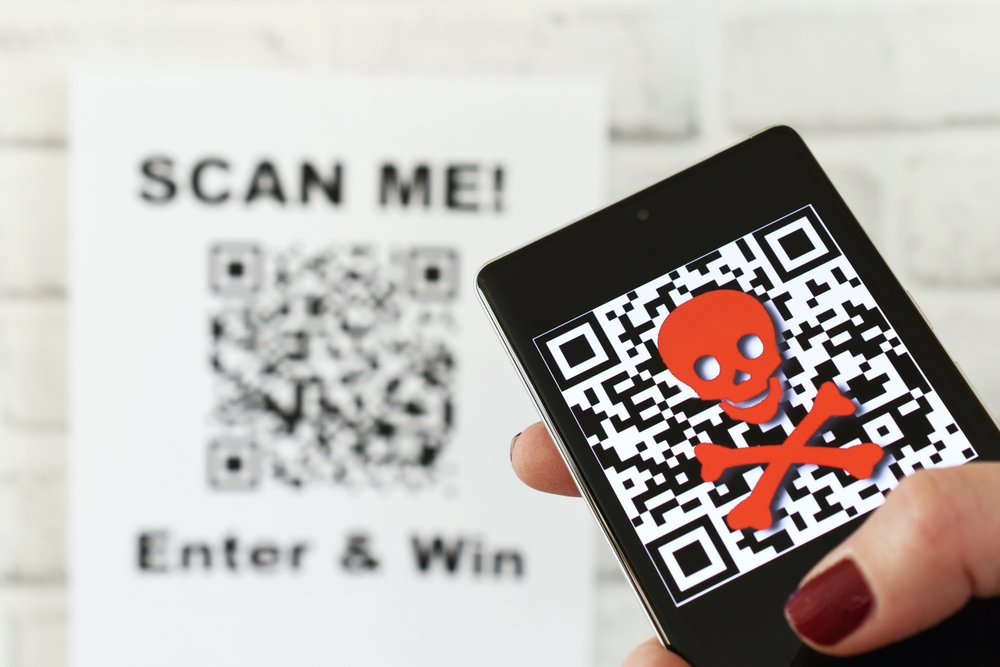
QR code phishing attacks, including quishing and QRLJacking, have seen a dramatic 587% increase from August to September 2023, with threat actors extracting login information from users. This social engineering tactic takes advantage of the trust in QR codes and the routine nature of security updates. The prevalence of quishing is a testament to the […]
Huawei, Honor, and Vivo devices are displaying false security alerts urging the deletion of the Google app due to a supposed TrojanSMS-PA malware, but Google denies that its app triggered the alerts.
The Wiki-Slack attack relies on crafting a legitimate footnote in a Wikipedia article and exploiting Slack’s rendering of the shared page’s preview to generate a hidden malicious link.
The organization has confirmed that it is a cybersecurity incident, and while there is no evidence of compromised personal information, it may take several days to fully restore normal operations.
The manufacturing sector is particularly vulnerable to IoT malware attacks, experiencing an average of 6,000 attacks per week according to Zscaler, which can disrupt critical OT processes and pose long-term challenges for security teams.
The order directs the National Institute of Standards and Technology to establish new standards for red-team testing and the Department of Health and Human Services to create a safety program for AI in healthcare.
The compromised website injected malicious content, including overlays promoting software serial keys, which resulted in misleading ads being automatically generated by Google Ads.
Though it shares strong similarities, Hunters International denies being the same group as Hive, claiming to have purchased the source code from them, and focuses on stealing data rather than encryption.