The Biden administration has considered an Energy Star type of consumer labeling program a key part of an effort to strengthen the nation’s cyber infrastructure following the SolarWinds and Colonial Pipeline attacks.
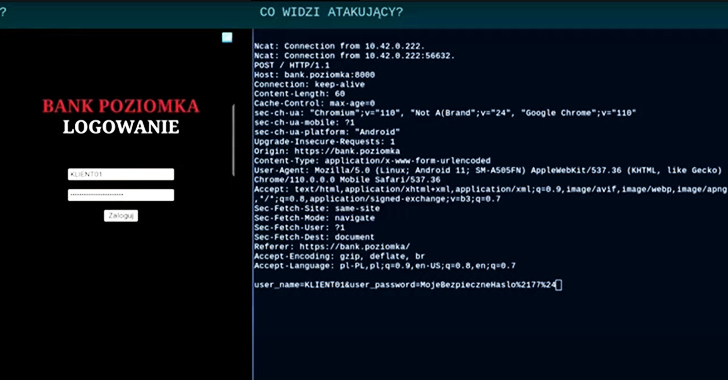
Operating as part of a Man-in-the-Browser (MITB) attack, the web injects allow cybercriminals to manipulate the content of legitimate web pages in real time, bypassing the TLS protocol.
The forensic investigation confirmed that there had been unauthorized access to files containing the protected health information of patients, some of which may have been obtained by the hackers.
For the past decade, millions of emails destined for .mil US military addresses were actually directed at .ml addresses, that being the top-level domain for the African nation of Mali, it’s claimed.
The average number of scam resources per brand across all regions and industries more than doubled year-on-year in 2022, up 162%, according to Group-IB. Additionally, the total number of scam pages detected in 2022 was more than thrice in 2021.
Cybersecurity researcher Jeremiah Fowler discovered a non-password-protected database containing approximately 2.3 million records associated with multiple dating applications.
Threat actors are taking advantage of Android’s WebAPK technology to trick unsuspecting users into installing malicious web apps on Android phones that are designed to capture sensitive personal information.
US-based enterprise software firm JumpCloud says a state-backed hacking group breached its systems almost one month ago as part of a highly targeted attack focused on a limited set of customers.
Researchers with Veriti are warning about “over 700 domains related to Threads being registered daily” in recent weeks, offering an Android version of the app for download outside of Google’s official app store.
Tracked as CVE-2023-38203 (CVSS score of 9.8), the flaw is described as “deserialization of untrusted data” in ColdFusion versions 2023, 2021, and?2018. This allows an attacker to use specially crafted data to trigger the execution of arbitrary code.