APIs are being used more than ever by businesses to build and provide better sites, apps, and services to consumers. However, if APIs are not managed or secured properly, they can be exploited by hackers to steal sensitive information.
Volt Typhoon is using compromised routers as a command-and-control network and deploying a new web shell called “fy.sh” on targeted Cisco routers, indicating a highly active and sophisticated operation.
German technology manufacturer Bosch has fixed a vulnerability in its popular line of smart thermostats that allowed attackers to replace the device firmware with a rogue version.
Purple team assessments, where red and blue teams collaborate, can provide a more comprehensive approach to security assessments, but they need to evolve to account for the multitude of attack technique variants.
Nearly 17,000 people had their personal information exposed in a ransomware attack on Fincantieri Marine Group. The attack, which occurred in April 2023, caused production issues and disrupted the company’s computer systems.
The Ministry of Foreign Affairs for Saudi Arabia reportedly experienced a major data breach, exposing the personal information of over 1.4 million employees, including names, contact details, and job titles.
Phishing scams in the UAE are on the rise, with fake websites posing as legitimate authorities and tourist sites. Scammers are using black hat SEO techniques to manipulate search engine rankings and promote fraudulent websites.
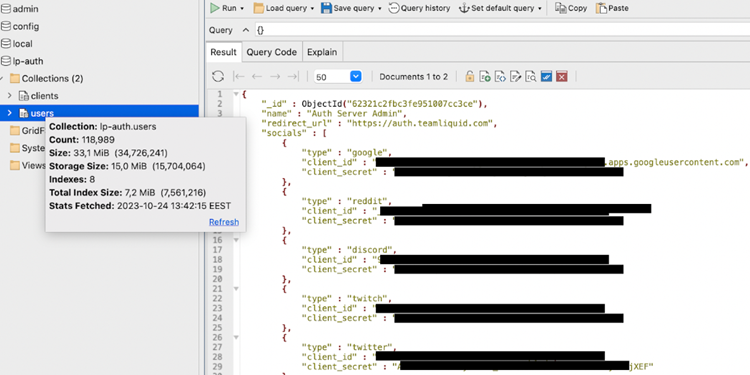
Liquipedia, an e-sports platform run by Team Liquid, experienced a data breach that exposed users’ email addresses and other details. The breach was caused by a publicly accessible and passwordless MongoDB database.
The Kansas state court system is recovering from a ransomware attack that occurred in October. The attack, carried out by a Russian ransomware gang, disrupted the operations of the court system for weeks and forced officials to use paper records.
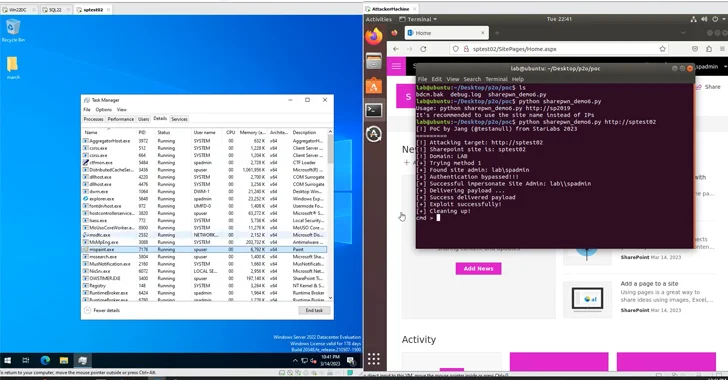
The privilege escalation flaw (CVE-2023-29357) allows attackers to gain administrator privileges by bypassing authentication, potentially leading to unauthorized access and control.