Passkeys in Bitwarden are generated using the PRF WebAuthn extension, which derives a unique encryption key from the passkey and enhances security. The passkey feature is currently in beta and available in Chromium-based browsers.
Researchers from Qualys have warned of a new wave of job scams on Facebook’s Meta platform. Scammers are using Facebook ads to lure users with offers of remote work and then stealing their personal data and banking credentials.
Cybersecurity researchers warn that the recent attacks on Denmark’s energy sector highlight the need for critical infrastructure organizations across Europe to remain vigilant against exploits targeting unpatched network infrastructure devices.
The leaked data, containing names, phone numbers, and addresses, appears to be accurate according to users listed in the file. Customers should be cautious of potential smishing attacks and the misuse of their information for fraudulent purposes.
The complexity of attributing cyber incidents to specific entities, such as nation-states or criminal groups, poses challenges when applying exclusions in insurance policies.
The World Economic Forum’s Global Risks Report 2024 highlights the increasing threat of cyber threats, with misinformation and disinformation being identified as the most severe risk globally.
The NCSC-FI has warned of increased Akira ransomware attacks in December. These attacks targeted companies in Finland and involved wiping backups, making it difficult for victims to recover their data without paying a ransom.
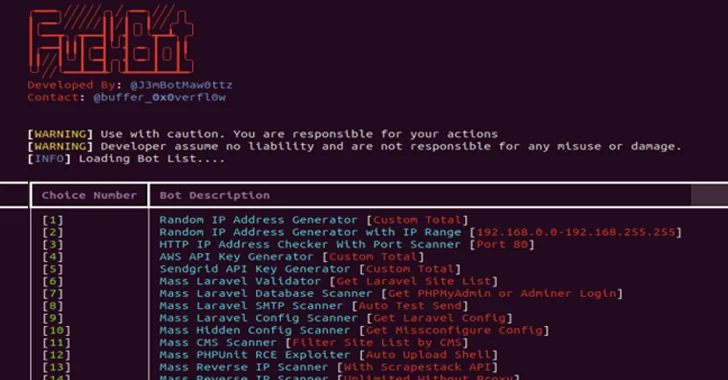
A new Python-based hacking tool called FBot has been discovered, targeting web servers, cloud services, content management systems, and SaaS platforms like Amazon Web Services and Microsoft 365.
MC2 Security Fund has completed its acquisition of Trustwave, a managed security services provider, expanding its reach and placing Trustwave in front of Chertoff Group customers in the commercial and public sectors.
Smaller organizations are increasingly reliant on cloud and online services, making them vulnerable to cyber threats. The guide provides practical advice on choosing the right service, securing user accounts, and recovering from a cyberattack.