The cybersecurity firm ClearSky identified the tools used, including the No-Justice wiper and a PowerShell code. The malware had a valid digital signature, making it appear legitimate.
This incident is part of a larger-scale social engineering campaign targeting verified X accounts on Twitter, highlighting the vulnerability of high-profile accounts to cryptocurrency scams and phishing attacks.
The backdoor, SpectralBlur, shares similarities with the KANDYKORN malware family attributed to North Korean threat actors and showcases their evolving tactics to infiltrate industries like cryptocurrency and blockchain.
The expansion of the FBI’s cyber program reflects a shift towards a proactive approach, focusing on disrupting cybercriminal operations rather than just investigating after the fact.
Bill Lou, co-founder of Nest Wallet, a cryptocurrency wallet startup, lost $125,000 to a crypto scam. He fell victim to a phishing attack after visiting a fraudulent website that appeared to be a legitimate crypto airdrop platform.
The funding opportunity is open to public and private stakeholders, universities, and DOE’s National Laboratories, and will focus on developing innovative solutions to strengthen the resilience of America’s energy systems.
AT&T Alien Labs discovered an ongoing campaign that delivers the AsyncRAT to targeted victims. The threat actor behind the campaign has been active for at least 11 months, using phishing emails and malicious JavaScript files to distribute the RAT.
The company claims that users negligently recycled and failed to update their passwords, allowing attackers to launch a credential stuffing campaign. Nearly 7 million customers’ information was accessed, including genealogy data.
The CNMF, composed of 39 joint cyber teams with over 2,000 military and civilian personnel, is a vital component of Cyber Command’s operations and has been authorized to become a permanent organization.
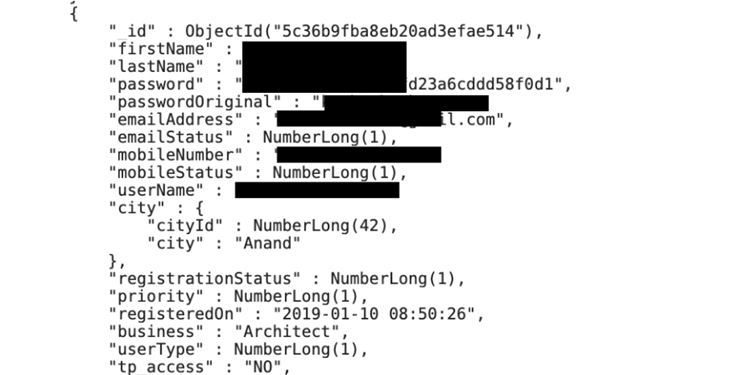
The MyEstatePoint Property Search app, developed by NJ Technologies in India, left a publicly accessible MongoDB server containing sensitive information such as names, plain-text passwords, email addresses, phone numbers, and more.