The Russia-linked hacker group Anonymous Sudan claimed responsibility for the DDoS attacks, targeting OpenAI due to its support for Israel and alleged bias in ChatGPT against Palestine.
The breach exposed sensitive patient data, including names, birthdates, addresses, medical information, and potentially Social Security numbers, emphasizing the risk of identity theft and healthcare fraud.
A new malvertising campaign has been observed wherein threat actors are copying a legitimate Windows news portal to promote a malicious installer for the popular processor tool CPU-Z. Based on the infrastructure, domain names, and cloaking templates used, researchers believe the incident is part of a larger malvertising campaign targeting other utilities such as Notepad++, […]
A new set of malicious Python packages has been discovered on the Python Package Index (PyPI) repository. These packages masquerade as harmless obfuscation tools but contain a malware called BlazeStealer. The campaign started in January 2023 and includes eight packages. Developers must stay alert and thoroughly assess the reliability and safety of packages before incorporating […]
The attack was not driven by military necessity but rather aimed to increase the psychological toll of the war, showcasing Russia’s focus on disrupting and degrading military readiness through cyber means.
The vulnerability, tracked as CVE-2023-47246, allows for arbitrary code execution and has been exploited by a threat actor known as Lace Tempest, who is associated with the deployment of Cl0p ransomware.
The North Korea-based BlueNoroff APT group has been linked with a new malware strain that is being used to target macOS systems. Dubbed ObjCShellz, the malware shares similarities with the RustBucket malware campaign, which came to light earlier this year.
The company revealed on Tuesday that a “potential security incident” discovered on November 3 involved unauthorized access to a Sumo Logic AWS account through the use of compromised credentials.
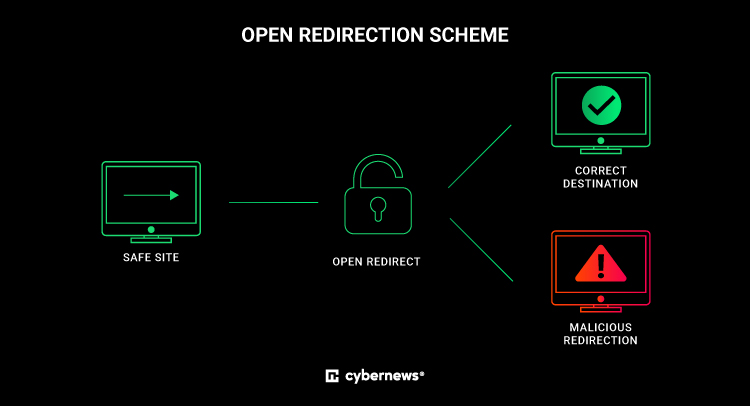
“The vulnerability can be exploited by attackers to trick users into visiting malicious websites or phishing pages by disguising the malicious URL as a legitimate one,” Cybernews researchers explained.
The malware runs a Discord bot and enables the threat actor to harvest a wide range of information, including passwords from web browsers and screenshots, execute arbitrary commands, encrypt files, and deactivate Microsoft Defender on the host.