Microsoft fixed a zero-day vulnerability in June, but the company did a poor job. Security researchers from Google’s Project Zero showed that attackers could still use the zero-day, despite the patch.
Yesterday, Wasabi users suddenly found that they could no longer access their storage buckets hosted on the wasabisys.com domain as one of its endpoints was used to host malware.
Microsoft says that the end goal of the SolarWinds supply chain compromise was to pivot to the victims’ cloud assets after deploying the Sunburst/Solorigate backdoor on their local networks.
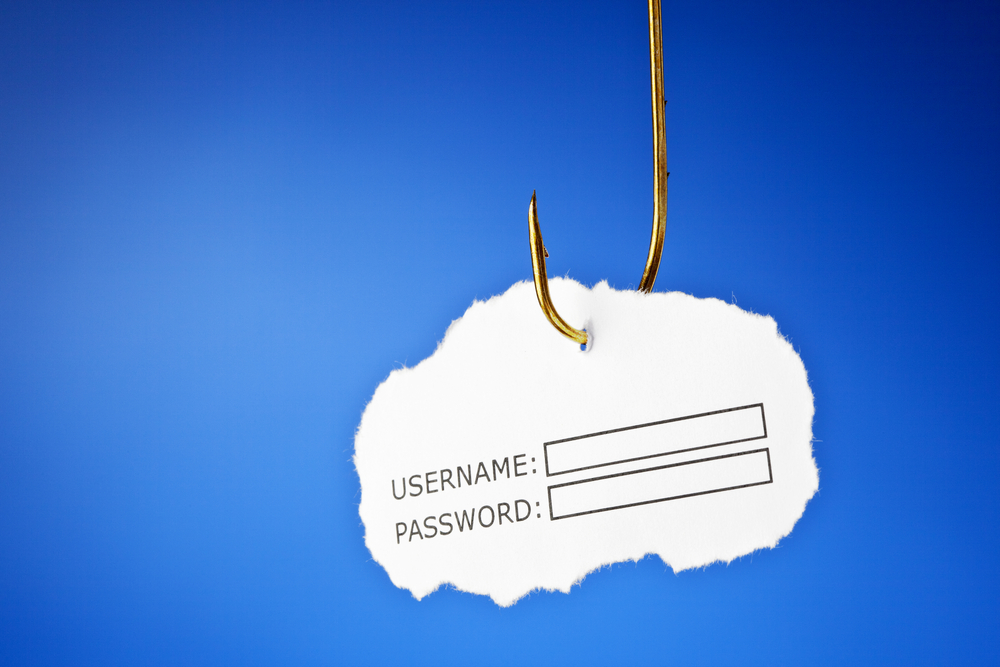
An employee of Freedom Finance fell victim to a phishing email, resulting in the loss of data of 16,000 clients from 2018. The attack also disrupted the internal network of the company.
With a large user base, it makes it quite easy for cybercriminals to publish malicious browser extensions that perform illicit activities, including spying and data theft, among others.
Four nation-state-backed APTs abused Pegasus phone-surveillance solution to target 36 Al Jazeera members by exploiting a zero-day in iPhones, in an espionage attack.
A threat intelligence analyst first spotted on a popular hacking forum a threat actor that is selling a database allegedly containing the database of the Italian mobile service provider Ho mobile.
Zero trust architecture is the opposite of the old “trust, but verify” methodology—instead, it’s a risk management approach that translates to: “trust nothing and record everything.”
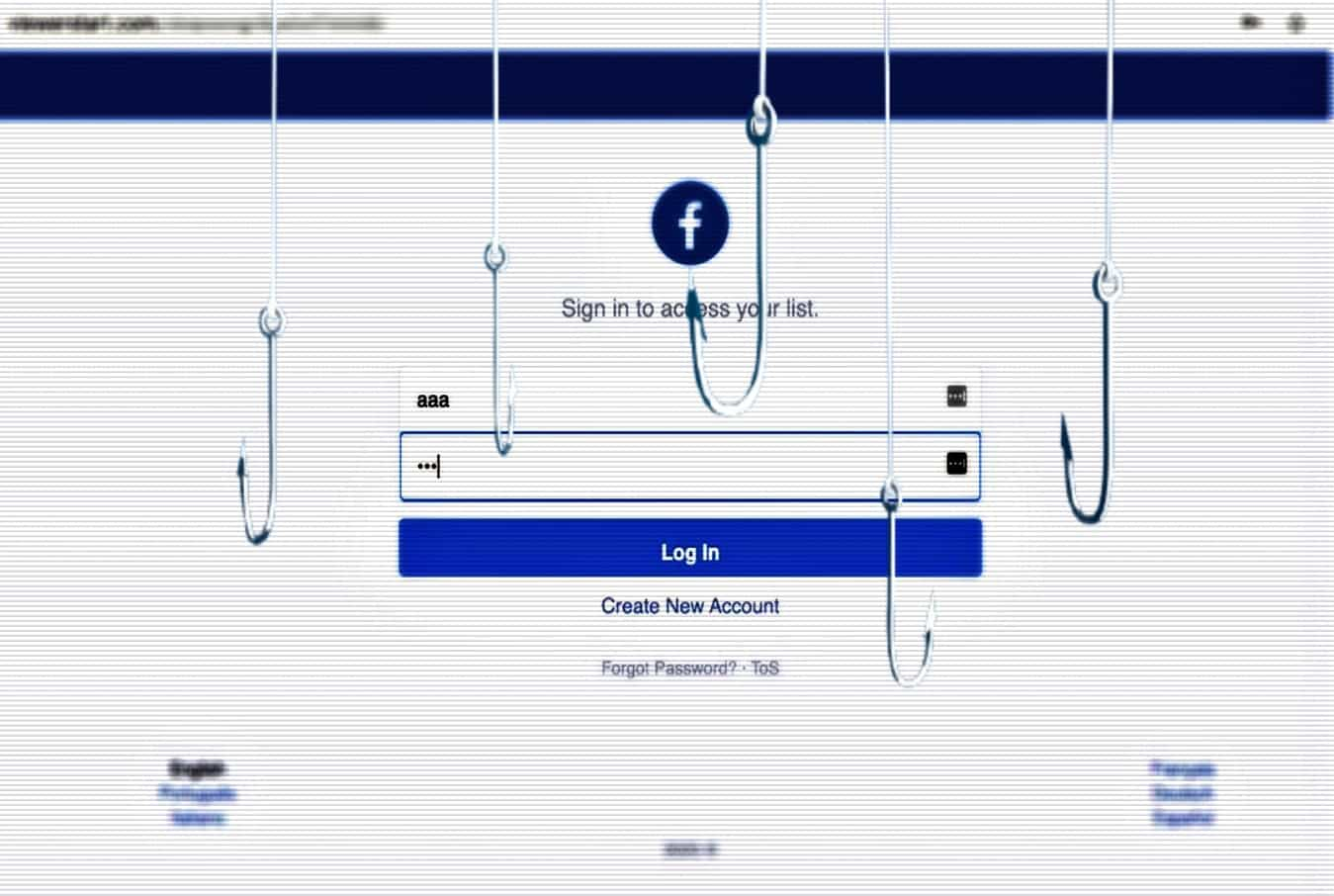
The Facebook users targeted span from a number of countries including Egypt, the Philippines, Pakistan, and Nepal with more than 615,000 of them being affected in totality.
Last week’s Brexit deal solidifies the terms under which the United Kingdom will leave the EU. But the issue of data transfers remains open, with great potential for confusion among privacy officers.