SolarWinds Orion products (affected versions are 2019.4 through 2020.2.1 HF1) are currently being exploited by malicious actors. This tactic permits an attacker to gain access to network traffic management systems.
The attacker’s post-compromise activity leverages multiple techniques to evade detection and obscure their activity, but these efforts also offer some opportunities for detection.
Unit 42 researchers have been tracking the threat group AridViper, which has been targeting the Middle Eastern region, and identified a new information stealer with relations to the MICROPSIA malware.
Google has announced the launch of a knowledge base called XS-Leaks to help web browser developers and security engineers prepare defense mechanisms against rising side-channel threats.
Manufacturers are increasingly being targeted not just by traditional malicious actors such as unorganized cybercriminals, but by competing companies and nations engaged in corporate espionage.
Security researchers have uncovered a critical flaw in Microsoft Teams that could allow an attacker to access confidential conversations and files from the communications service.
Cybercrime against digital media and entertainment organizations is on the rise. Hackers formulate new and innovative ways to defeat security measures and controls to pilfer sensitive data.
Guardicore first spotted the attack back in January 2020. After that, it witnessed a total of 92 attacks emanate from 11 IP addresses, with most based in Ireland and the UK at the time of analysis.
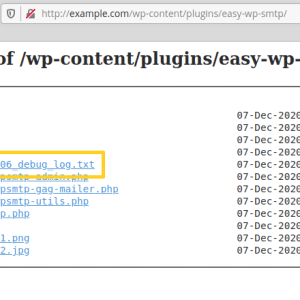
The zero-day vulnerability affects WP SMTP 1.4.2 and earlier versions, it resides in a feature that creates debug logs for all emails sent by the site and store them in the installation folder.
It’s still unclear what kind of information might have been compromised. Much of the city’s files — budget documents, building plans, and council minutes — are records available to the public under the Missouri Sunshine Law.