The Standard version of Safe Browsing has been updated to support real-time data lookup, as many unsafe sites exist for less than 10 minutes, slipping through locally stored lists.
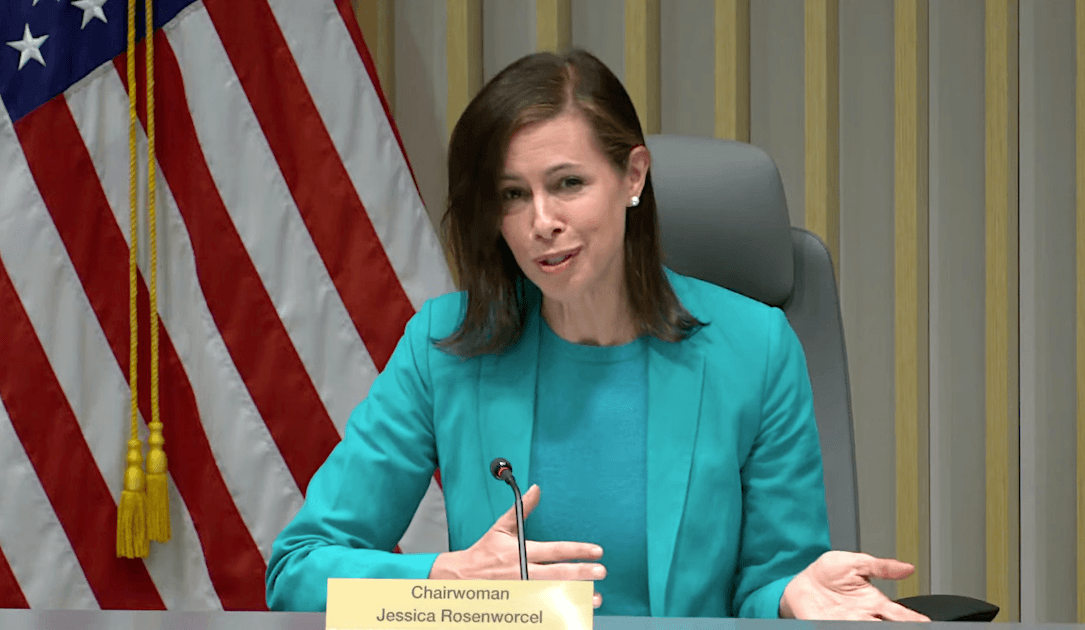
The FCC intends for the label to apply to a range of products, including home security cameras, internet-connected appliances, fitness trackers, garage door openers, baby monitors, and voice-activated devices.
The US House of Representatives has passed a bill requiring ByteDance, the parent company of TikTok, to sell the social media platform within 165 days or face a complete ban in the United States.
StopCrypt ransomware, also known as STOP Djvu, has evolved with a new multi-stage execution process involving shellcodes to evade security tools. Unlike ransomware operations targeting businesses, StopCrypt primarily targets consumers.
Arcserve has addressed critical security vulnerabilities (CVE-2024-0799, CVE-2024-0800) in its Unified Data Protection (UDP) solution, which could be exploited to upload malicious files to the underlying Windows system.
Threat actors are exploiting legitimate digital document publishing (DDP) sites to host phishing lures, making it harder for traditional security controls to detect and block these attacks.
The stolen data includes sensitive personal details such as full name, date of birth, social security number, and contact information, posing a significant risk of identity theft and phishing.
The cyberattack on Change Healthcare, a UnitedHealth Group subsidiary, has underscored the growing cybersecurity challenge facing the healthcare sector. The outage has disrupted critical operations, impacting claims processing and patient records.
Rapid7’s decision to release details on the vulnerabilities led to immediate exploitation by attackers, according to JetBrains. The dispute arose from Rapid7’s objection to JetBrains’ preference for private patch releases and silent patching.
Following the disruption of the Qakbot botnet in August 2023, ransomware affiliates have transitioned to exploiting vulnerabilities as the primary method of delivering malware.