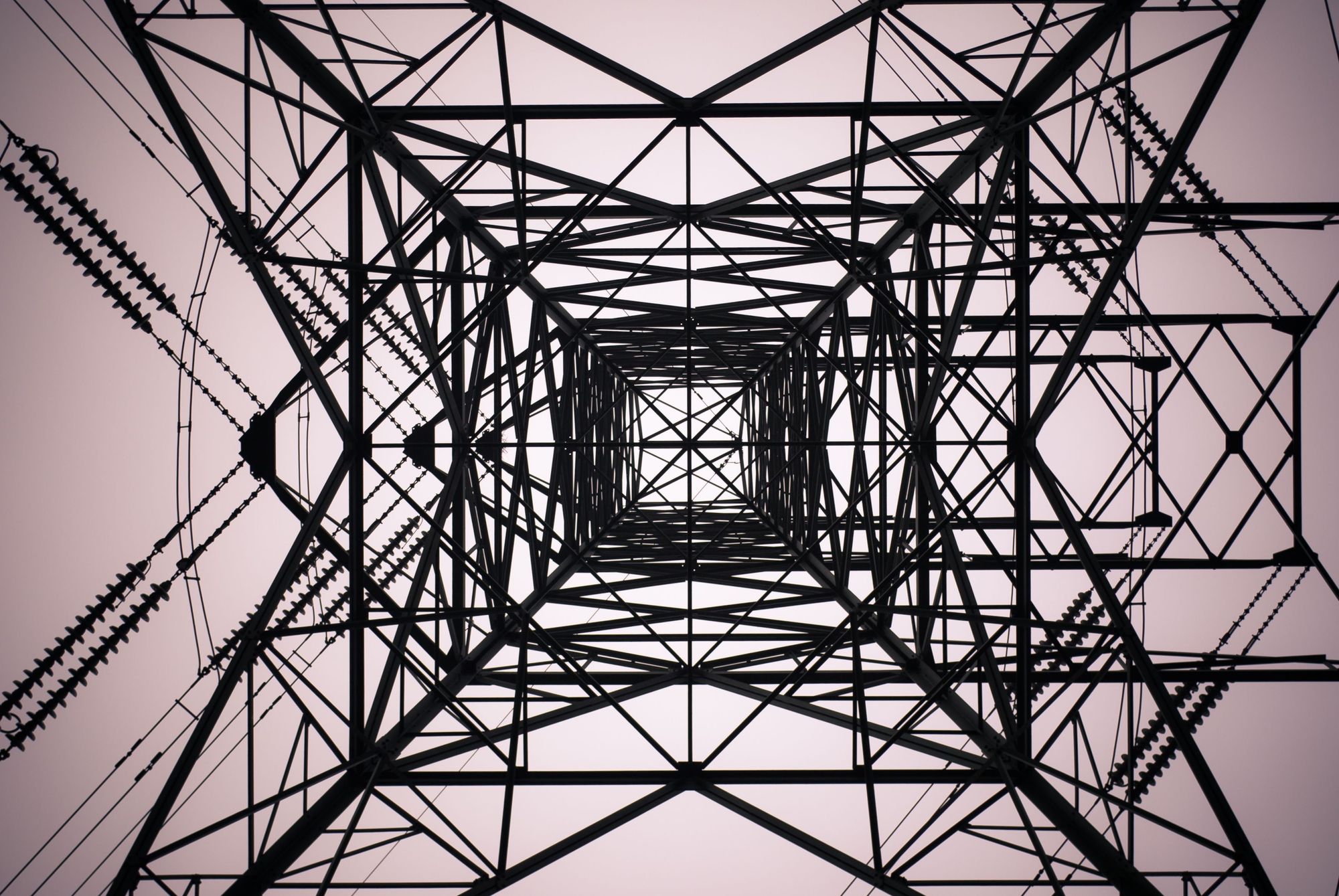
Researchers discovered that a solar grid responsible for 20% of the world’s solar power output, enough to power the entire United States, is at risk of being hijacked due to vulnerabilities in PV plant management platforms.
Recent findings indicate that the 7777 botnet (aka Quad7) has likely expanded, adding new bots with open port 63256, primarily including Asus routers. As of August 5, 2024, the total number of active bots stood at 12,783.
The malware attack flow involves luring users with fake websites imitating popular downloads, then executing PowerShell scripts to download and install malicious extensions that steal private data and control browser settings.
A fraudulent site resembling the official WinRar distribution platform is spreading malware. The fake website, win-rar[.]co, utilizes typosquatting to trick users who mistype the URL.
Quorum Cyber Incident Response team recently identified a new malware called SharpRhino utilized by the threat actor group Hunters International during a ransomware incident. The malware, written in C#, was distributed through a typosquatting domain posing as Angry IP Scanner.
Consumer Reports cautioned against relying too heavily on data removal services, as many fall short of expectations despite high costs. The study highlighted the need for better protection of consumer data and stricter regulations on data brokers.
The attack begins with a phishing email that directs recipients to what appears to be an Amazon account verification link. However, this link is a deceptive graphic hosted on Google Drawings, a component of the Google Workspace suite.
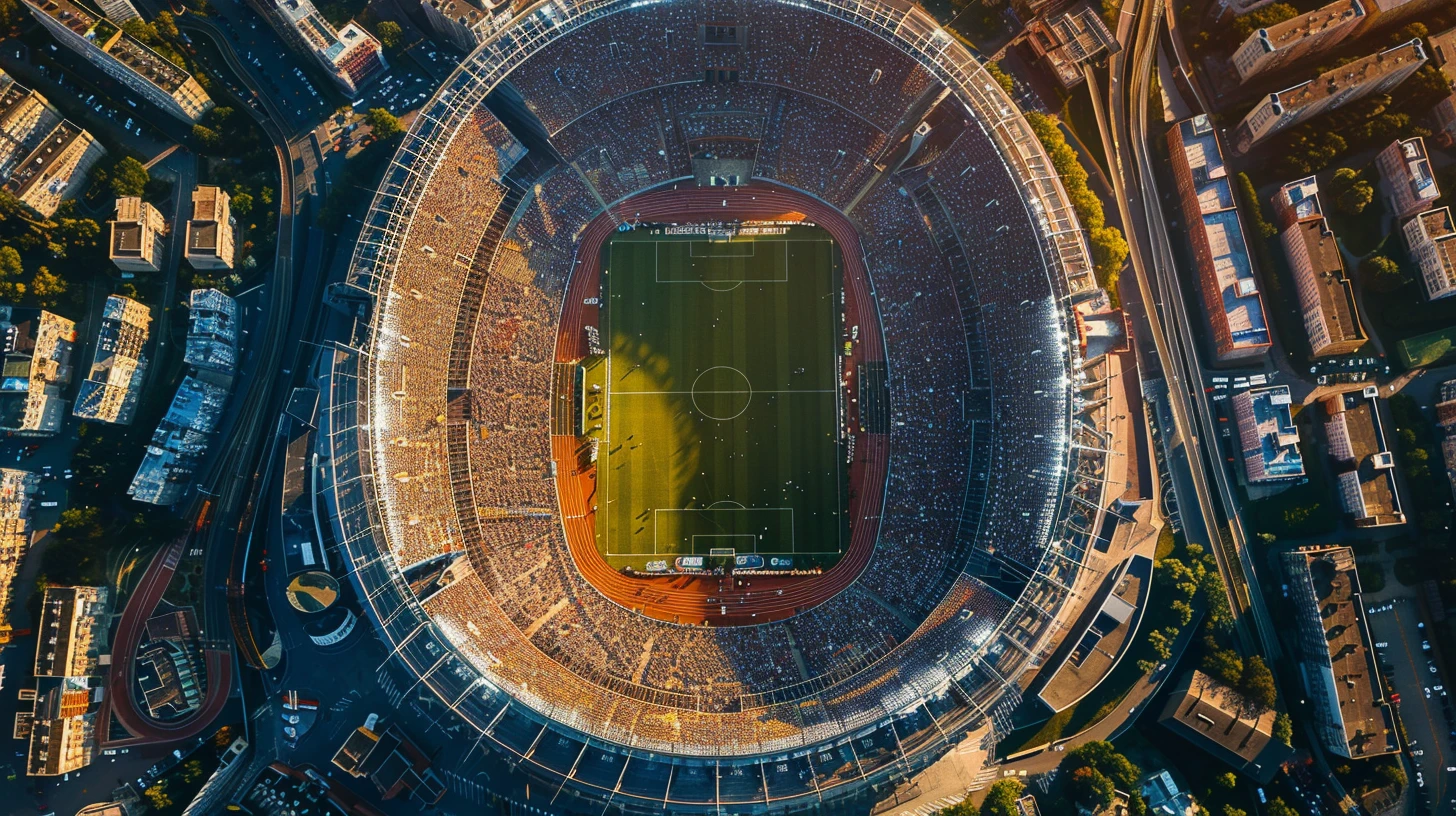
The sports and entertainment industries face unique cybersecurity challenges due to the rapid technological advancements being implemented. Cyber-physical systems like augmented reality and smart sensors increase security concerns.
A ransomware drill focused on healthcare called Operation 911 was conducted at Black Hat USA 2024 by Las Vegas law enforcement, the FBI, and Semperis. During the drill, a simulated ransomware attack targeted a fictitious hospital.
Kursk region in Russia was hit by a large-scale DDoS attack during Ukraine’s cross-border incursion, affecting government, business websites, and critical services. NetBlocks reported disruptions in internet connectivity linked to the attacks.